Akamai Noname API Security Integrating with .NET Application
In this blog, we will learn how to integrate the Akamai Noname API Security with a .NET application.
Introduction
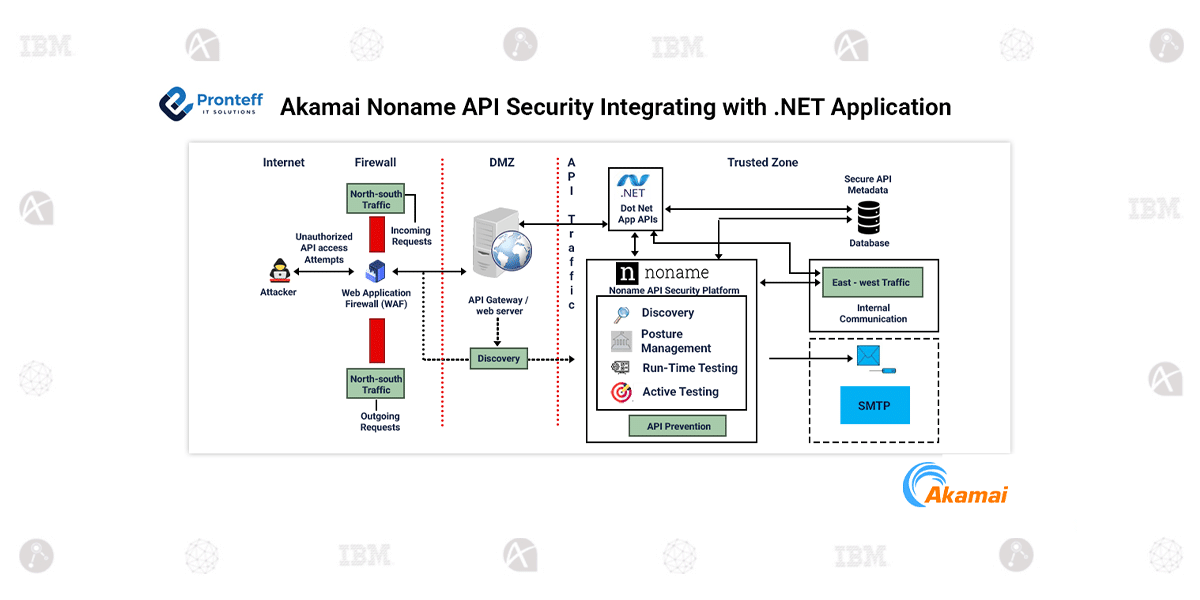
APIs play a central role in modern software architectures by enabling communication between applications, services, and external platforms. As organizations increasingly depend on APIs, ensuring their security becomes a major priority. Akamai Noname API Security provides a comprehensive platform designed to monitor API traffic, detect potential threats, and improve overall API visibility.
For environments running .NET or .NET Core applications on Microsoft IIS, Noname API Security can be integrated through a lightweight IIS native module. This module enables API traffic generated by IIS-hosted applications to be forwarded to the Noname security engine for analysis. As a result, organizations gain deeper insight into API usage and potential security risks without impacting application performance.
Overview of the Integration
The integration works by deploying a native module within the IIS web server environment. Once enabled, the module observes API traffic handled by the server and collects relevant request and response metadata. This information is securely transmitted to the Noname API Security engine for further evaluation.
To prevent performance degradation, the module operates asynchronously. Instead of inspecting each request in real time, it groups API data and sends it in batches. This approach allows applications to continue functioning normally while API traffic is analysed independently.
Integration Workflow
After installation, the module becomes part of the IIS processing pipeline. As API requests pass through the server, the module extracts key details such as endpoints, headers, and communication patterns. These data points are then forwarded to the Noname engine.
The security engine analyses the collected information to identify suspicious behaviour, including unauthorized access attempts, abnormal usage patterns, data exposure risks, or violations of security policies. This continuous analysis helps organizations detect and respond to potential API threats quickly.
Compatibility and Deployment Options
The IIS module is compatible with both .NET Framework and .NET Core applications. It also supports 32-bit and 64-bit environments and works with IIS application pools running in Integrated or Classic pipeline modes.
The module can be deployed at multiple levels within IIS, including the server level, website level, or application level, giving organizations flexibility in determining which services should be monitored.
Key Use Cases
- API Discovery: Identify all exposed and shadow APIs across environments.
- Posture Management: Detect unauthorized access attempts and abnormal API behaviour.
- Runtime Security Insights: Continuously monitor east-west traffic between internal services.
- Active Testing: Actively test APIs for vulnerabilities before exploitation.
- API Prevention: Enables enforcement of security policies by blocking or mitigating malicious API activity.
- Alerts: Generates alerts based on detected threats or policy violations and sends them to administrators via internal systems (e.g., SMTP).
By integrating Akamai Noname API Security with Microsoft IIS, organizations can strengthen API protection for their .NET applications.