HashiCorp Vault and the Practical Power of Secret Engines
In this blog, we will learn about Hashicorp Vault and the practical power of secret engines.
As organizations move toward cloud-native infrastructure, containers, and automation pipelines, managing sensitive data has become increasingly complex. Every application depends on credentials—database logins, API keys, encryption keys, certificates, and tokens. When these secrets are stored in configuration files or embedded in code, they create serious security risks. A single leak can expose entire systems.
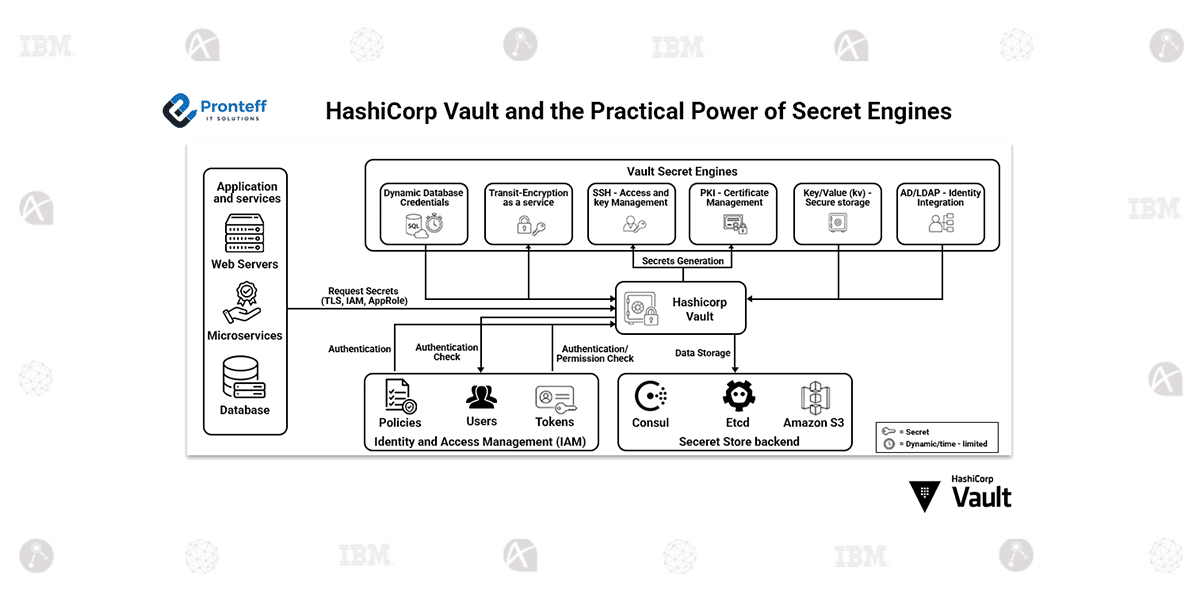
HashiCorp Vault addresses this challenge by acting as a centralized security control plane for secrets. Rather than scattering credentials across environments, Vault securely stores, generates, and manages access to sensitive information. What makes Vault especially powerful is its modular system, known as Secret Engines.
Secret Engines are components that handle different categories of secrets and define how they are created, accessed, and revoked. Let’s explore how they are used in real-world environments.
Dynamic Database Credentials
One of Vault’s most valuable features is its ability to generate credentials dynamically. Instead of using permanent usernames and passwords for databases, Vault can create temporary accounts whenever an application requests access.
For example, if a microservice needs to query a PostgreSQL database, Vault generates a unique username and password with limited permissions. These credentials automatically expire after a defined time. This eliminates the need for manual password rotation and drastically reduces the damage caused by credential leaks.
Cloud Access Key Management
Cloud environments rely heavily on access keys. Vault integrates with providers such as AWS and Azure to produce short-lived access credentials on demand. Rather than sharing long-term cloud keys among teams, organizations can issue temporary keys that expire automatically. This approach strengthens security while maintaining operational flexibility.
PKI and Certificate Automation
Managing SSL/TLS certificates across distributed systems can become overwhelming. Vault’s PKI Secret Engine functions as an internal certificate authority. It can issue, renew, and revoke certificates programmatically.
In service-to-service communication, especially within Kubernetes clusters, Vault can provide short-lived certificates that secure encrypted connections without requiring manual certificate distribution.
Secure Storage for Application Secrets
Vault also offers a key-value secrets engine for storing static data such as API tokens or third-party service credentials. Access to these secrets is governed by detailed policies, ensuring that users and services only retrieve what they are explicitly permitted to access.
Identity-Based Access Control
Security is not only about storing secrets but also controlling who can use them. Vault integrates with identity providers and supports policy-driven access control. Combined with auditing features, organizations gain visibility into who accessed what and when.
Final Thoughts
HashiCorp Vault is more than a password vault. It is a comprehensive secrets management platform designed for modern infrastructure. Through its Secret Engines, Vault enables dynamic credential generation, automated certificate management, and strict access governance. By replacing static secrets with controlled, short-lived access, organizations can significantly reduce risk while improving automation and scalability.