An introduction to GitOps and Secret Management with ArgoCD Operator and SOPS
Unlike FluxCD, which offers seamless integration, ArgoCD’s secret management requires additional configuration. ArgoCD, on the other hand, enables the integration of numerous well-liked GitOps community tools. I strongly suggest reading this blog post by Jann Fischer and Raffaele Spazzoli if you want to learn more about the many tools that are available and how they work.
This post will examine how to use the Kustomize plugin, often known as KSOPS, to connect Mozilla SOPS with Openshift Gitops Operator. We will use the Age tool to encrypt the file because it is preferred by the SOPS manual over PGP.
Describe KSOPS.
KSOPS, sometimes known as kustomize-SOPS, is a kustomize plugin for managing resources that are SOPS-encrypted. Although KSOPS can be used to decrypt any Kubernetes resource, it is most frequently used to decrypt ConfigMaps ands Kubernete Secrets. KSOPS’ main objective is to manage encrypted resources in a similar manner to how we handle Kubernetes manifests.
Requirements for beginning:
1. OpenShift 4 cluster
2. OpenShift CLI
3. Kustomize CLI
4. SOPS CLI
Install GitOps Operator
For details, refer to the OpenShift Gitops Operator Installation guide. Check to see if every pod in the openshift-gitops namespace is active:
$ oc get pods -n openshift-gitops Example output NAME READY STATUS RESTARTS AGE cluster-b5798d6f9-zr576 1/1 Running 0 65m kam-69866d7c48-8nsjv 1/1 Running 0 65m openshift-gitops-application-controller-0 1/1 Running 0 53m openshift-gitops-applicationset-controller-6447b8dfdd-5ckgh 1/1 Running 0 65m openshift-gitops-redis-74bd8d7d96-49bjf 1/1 Running 0 65m openshift-gitops-repo-server-c999f75d5-l4rsg 1/1 Running 0 65m openshift-gitops-server-5785f7668b-wj57t 1/1 Running 0 53m
Generate Age Key
To create a new key, install the Age tool and execute the command below:
$ age-keygen -o age.agekey Public key: age1helqcqsh9464r8chnwc2fzj8uv7vr5ntnsft0tn45v2xtz0hpfwq98cmsg
OpenShift Secret
The “openshift-gitops” project’s next step is to develop a secret:
cat age.agekey | oc create secret generic sops-age --namespace=openshift-gitops \ --from-file=key.txt=/dev/stdin
Now that custom tooling is available, we are prepared to update the ArgoCD custom resource.
ArgoCD with Custom Tooling
Edit the object by going to the ArgoCD link under the Red Hat OpenShift GitOps operator.
Change ArgoCD’s repository server settings as indicated below. In the following configuration, we are:
- installing KSOPS in a fresh initContainer under the custom-tools directory
- mounting the age private key to decrypt sensitive information
repo:
env:
- name: XDG_CONFIG_HOME
value: /.config
- name: SOPS_AGE_KEY_FILE
value: /.config/sops/age/keys.txt
volumes:
- name: custom-tools
emptyDir: {}
- name: sops-age
secret:
secretName: sops-age
initContainers:
- name: install-ksops
image: viaductoss/ksops:v3.0.2
command: ["/bin/sh", "-c"]
args:
- 'echo "Installing KSOPS..."; cp ksops /custom-tools/; cp $GOPATH/bin/kustomize /custom-tools/; echo "Done.";'
volumeMounts:
- mountPath: /custom-tools
name: custom-tools
volumeMounts:
- mountPath: /usr/local/bin/kustomize
name: custom-tools
subPath: kustomize
- mountPath: /.config/kustomize/plugin/viaduct.ai/v1/ksops/ksops
name: custom-tools
subPath: ksops
- mountPath: /.config/sops/age/keys.txt
name: sops-age
subPath: keys.txt
When you save, the openshift-gitops-repo-server pod should be rebuilt.
We are now prepared to test our modifications:
1. Configure SOPS via .sops.yaml
KSOPS relies on the SOPS creation rules specified in.sops.yaml for this example and testing. It is advised to just encrypt data and stringData values when using the following encryption regex to make encrypted secrets easier to read. As a result, non-sensitive fields like the name of the secret remain unencrypted and viewable by humans.
cat <<EOF > .sops.yaml creation_rules: - path_regex: apps/.*\.sops\.ya?ml encrypted_regex: "^(data|stringData)$" age: age1helqcqsh9464r8chnwc2fzj8uv7vr5ntnsft0tn45v2xtz0hpfwq98cmsg EOF
2. Create a local Kubernetes Secret:
cat <<EOF > secret.sops.yaml apiVersion: v1 kind: Secret metadata: name: mysecret type: Opaque data: username: YWRtaW4= password: MWYyZDFlMmU2N2Rm EOF
3. Encrypt with SOPS CLI:
sops --encrypt --in-place secret.sops.yaml
4. Define KSOPS kustomize Generator:
cat <<EOF > secret-generator.yaml apiVersion: viaduct.ai/v1 kind: ksops metadata: # Specify a name name: example-secret-generator files: - ./secret.sops.yaml EOF
5. Produce the customization.yaml file and push all the modifications to the Git repository. Kostomize plugins can be found here:
cat <<EOF > kustomization.yaml generators: - ./secret-generator.yaml EOF
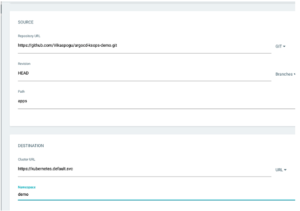
6. Utilize your repository to create a new Argo application using the Argo console.
7. Argo will download the most recent commit and apply the modifications.
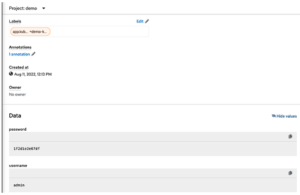
8. Check the OpenShift console to confirm the modifications were applied.
Conclusion
In conclusion, SOPS is a powerful tool for securely maintaining sensitive data, and when combined with ArgoCD, it offers a smooth solution to handle secrets in the same manner we manage the other Kubernetes manifests.