Enhancing Ray Cluster Security in Red Hat OpenShift AI 3.0.
In this blog, we will learn how to enhance ray cluster security in Red Hat OpenShift AI 3.0.
The adoption of Ray as a framework for scalable AI and machine learning workloads continues to grow rapidly. While Ray enables powerful distributed computing capabilities, its official guidance makes one thing clear: responsibility for securing deployments ultimately lies with developers or platform operators.
At Red Hat OpenShift AI, delivering a reliable, enterprise-ready environment for advanced AI workloads is a core priority. As part of this commitment, OpenShift AI 3.0 introduces enhancements to the Controlled Network Environment (CNE) for Ray clusters, delivered natively through KubeRay.
CNE represents a platform-enforced security model that automatically applies recommended Ray security practices, helping protect clusters from the moment they are created.
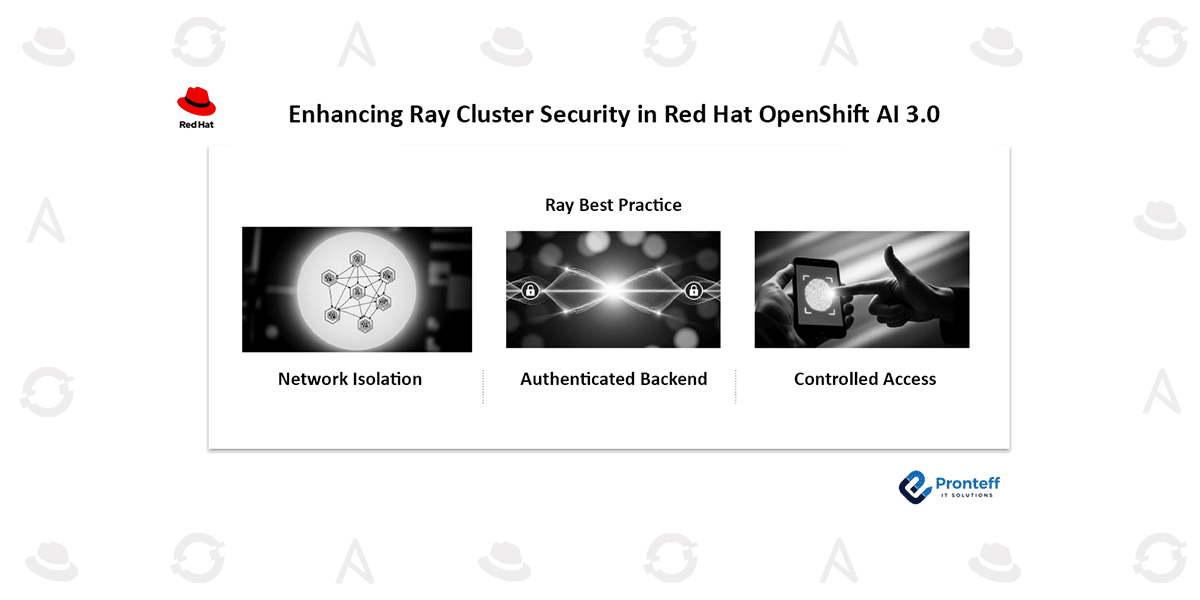
The Three Foundations of the Controlled Network Environment
The controlled network environment is built around three essential security capabilities that are automatically enforced for every Ray Cluster deployed in OpenShift AI 3.0:
Network Isolation
OpenShift AI simplifies network protection by automatically applying Kubernetes-native network policies through the KubeRay Operator.
These policies restrict communication strictly to components inside the same Ray Cluster, preventing unauthorized traffic from other pods and establishing a clearly defined security boundary around the workload.
Authenticated Backend with mTLS
OpenShift AI now enforces secure internal communication using mutual Transport Layer Security (mTLS).
This approach ensures that all services within a Ray Cluster both authenticate each other and encrypt data exchanged internally. Certificate management is automated using cert-manager, removing operational overhead by handling certificate generation, renewal, and secret management automatically.
For users working with the codeflare-sdk client, existing workflows continue to function without modification.
Controlled User Access
OpenShift AI 3.0 also introduces improvements to how users securely access the Ray dashboard.
Access control is now integrated with the platform’s updated authentication framework built on the Gateway API. Instead of requiring multiple logins, users authenticate once through their OpenShift AI session and gain seamless access across services, creating a more consistent and secure user experience.
Platform Improvements Beyond Security
These enhancements deliver benefits that extend beyond stronger protection:
Simplified architecture
Core security capabilities—including network isolation and mTLS configuration—are now embedded directly into the KubeRay reconciler. This reduces architectural complexity and accelerates future feature development.
Enhanced user experience
Unified authentication streamlines access to Ray services, improving usability while maintaining strict security controls.
Security is enforced by default
Every Ray Cluster deployed in OpenShift AI automatically inherits the Controlled Network Environment configuration, ensuring consistent security without manual setup.
Contributing Back to the Community
The redesign of the Controlled Network Environment also prepares the groundwork for upstream collaboration. Red Hat is actively working toward contributing these improvements to the broader KubeRay open-source ecosystem.
What’s Next
With OpenShift AI 3.0, Red Hat delivers a production-grade Ray platform where strong security is built in—not added later. Organizations can now deploy distributed AI workloads with confidence, knowing that protection, isolation, and authenticated access are enabled by default.
Start building and scaling your Ray workloads on OpenShift AI today.