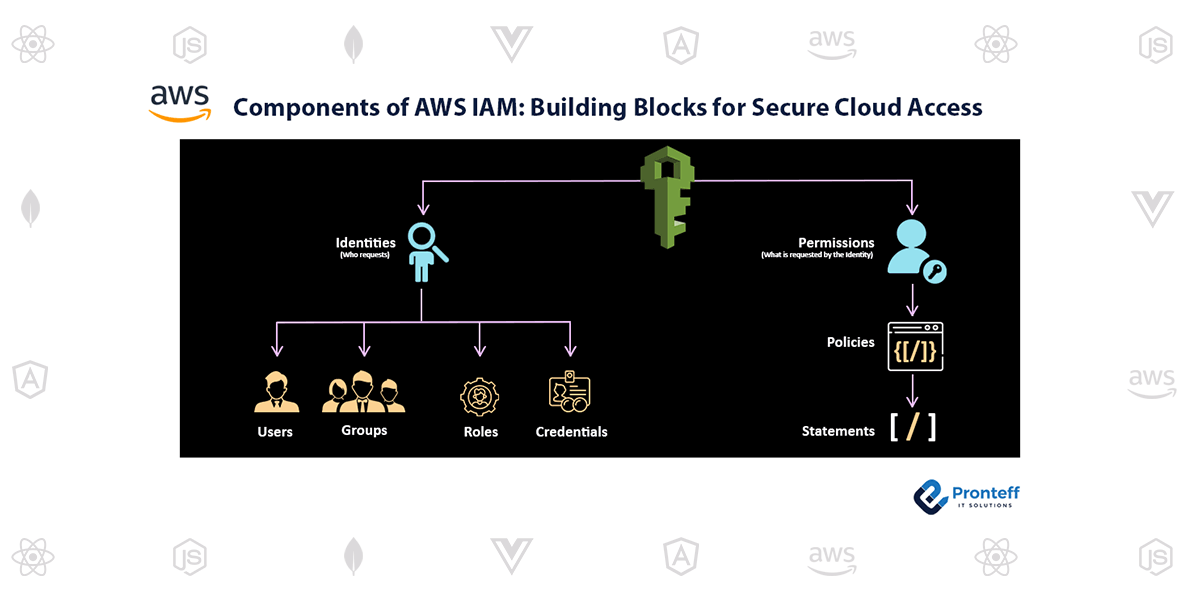
Components of AWS IAM: Building Blocks for Secure Cloud Access
In the world of cloud computing, security plays a vital role. AWS Identity and Access Management (IAM) is a powerful service provided by Amazon Web Services (AWS) that helps you manage and control access to your AWS resources. IAM consists of several components that work together to ensure secure and granular access control. In this blog post, we will explore the key components of AWS IAM and their importance in building a robust security posture.
Users
Users are the individuals or entities that interact with your AWS resources. Each user is assigned a unique identifier and AWS credentials, consisting of an access key and a secret access key. Users can be categorized into different groups, making it easier to manage permissions and access control. IAM users are the foundation of access management in AWS, and it is crucial to set up individual user accounts for each person or system that requires access.
Groups
Groups are a way to manage and assign permissions to multiple users simultaneously. Instead of configuring permissions for each user individually, you can create groups and assign appropriate policies to them. For example, you can have a “Developers” group with policies allowing access to specific EC2 instances and an “Administrators” group with policies granting full administrative privileges. This simplifies the management of permissions and makes it easier to enforce consistent access control across your AWS environment.
Roles
IAM roles are similar to users, but they are not associated with a specific identity. Roles are meant to be assumed by trusted entities such as AWS services, applications, or EC2 instances. By assigning roles to these entities, you can grant them specific permissions to access AWS resources without the need for access keys. Roles provide an additional layer of security by eliminating the need to embed long-term credentials within your applications or instances.
Policies
Policies define what actions are allowed or denied on AWS resources. They are JSON documents that specify the permissions granted to users, groups, or roles. IAM policies can be attached directly to users, groups, or roles, or they can be associated with AWS resource-based policies. Policies follow the principle of least privilege, allowing you to grant only the necessary permissions required to perform specific tasks. AWS provides pre-defined policies for common use cases, and you can also create custom policies tailored to your specific requirements.
Permissions Boundary
An advanced IAM feature called a permissions boundary allows you to limit the number of permissions that an entity (user or role) can have. By setting a permissions boundary, you can prevent users or roles from exceeding certain permissions, even if they are assigned additional policies or permissions directly. This feature is useful when you want to restrict the actions that a user or role can perform, providing an extra layer of control and reducing the risk of unintended privilege escalation.
Conclusion
AWS IAM components form the building blocks of a secure and well-managed cloud environment. Understanding and effectively utilizing these components enable you to implement granular access control, enforce the principle of least privilege, and enhance the overall security posture of your AWS resources. By leveraging users, groups, roles, policies, and permissions boundaries, you can ensure that only authorized entities have the appropriate level of access to your critical resources.
Regularly review and update IAM configurations as your organization’s needs evolve. Continuous monitoring and auditing of IAM policies and access patterns are essential to maintain a robust and secure AWS environment.