Early Software Development Lifecycle Security Implementation with Shift Left Strategy
Here in this blog, we are going to learn how to do early software development Lifecyle Implementation with Shift Left Strategy.
Developing and deploying applications is frequently given top priority. The “shift left” technique is used by developers to enhance application security. With this approach, security procedures and testing are incorporated early on in the development cycle. This strategy is crucial when using OpenShift and containerization.
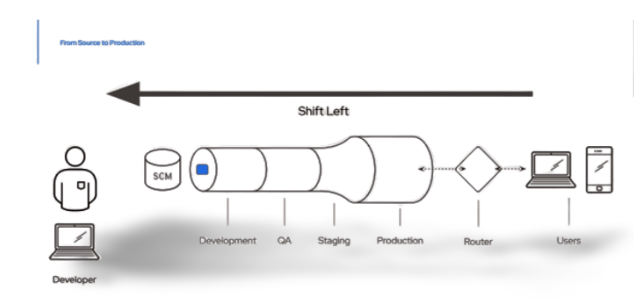
To begin understanding shift left, let’s define “developer flow.” The development process known as “developer flow” involves the developer moving through two “loops” that stand in for the pre-release stages. The “inner loop,” or creative stage, is where the developer writes the code. After then, the “outer loop” is made accessible for production. The illustration below shows this.
Inner loop: The inner loop is a cycle of code development, compiling, running, and debugging that occurs frequently. The emphasis is on implementing tiny changes, testing them, and swiftly gathering feedback. Rapid development and continuing code change validation are key.
Outer loop: On the other hand, it’s crucial to have a well defined approach for decision-making and progress monitoring when it comes to the outer loop. This include managing high-level issues, coordinating system integrations, and assuring compliance. To keep everything on track, establish regular checkpoints, evaluations, and feedback loops.
Furthermore, prioritizing open source dependencies is crucial for security and integrity reasons, particularly in light of recent vulnerabilities. The keys to reaching your goals include being informed, responding quickly to security advisories, and using tools like Software Bills of Material (SBOM) to efficiently manage components.
A crucial tactic that emphasizes incorporating security procedures early in development is the shift left method. Organizations can spot vulnerabilities early on and take action to fix them, lowering the likelihood that serious security problems will develop later.
The inner loop, which concentrates on the code and dependency security aspects of application development, is a key component of the shift left technique. Security procedures like secure coding techniques, code reviews, static and dynamic code analysis, and automated vulnerability scanning are incorporated into developers’ work processes. Developers can promote secure coding techniques and lessen the possibility of introducing exploitable holes by proactively addressing security problems within the inner loop. This helps developers find and fix vulnerabilities quickly.
Unit testing, integration testing, and security-focused testing are all included in the inner loop’s integration of quality assurance and security testing operations. Early security testing integration allows developers to proactively find and fix flaws, ensuring that the application runs safely and according to plan.
The shift left approach also promotes cooperation and communication between the development and security teams. By integrating security specialists from the beginning, developers gain knowledge about security best practices, threat modeling, and secure design principles. This cooperative strategy encourages the development team to adopt a security-conscious mindset and makes it easier to identify and mitigate security problems before they become serious.
In general, the shift left method prioritizes security concerns during the development process. Organizations may develop more secure applications, lessen the potential effects of security breaches, and ultimately offer higher-quality software that prioritizes safeguarding private information and sensitive data by integrating security principles into the inner loop.