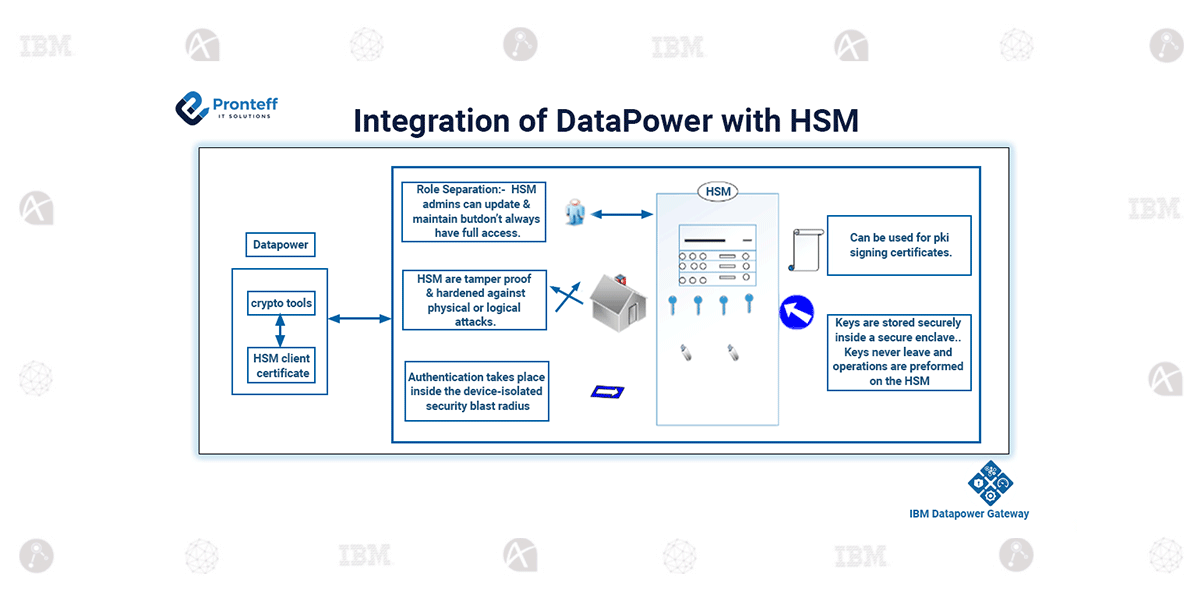
Integration of DataPower with HSM
Here in this blog, we will learn about the integration of DataPower with HSM.
What is HSM
HSM stands for hardware security module. It’s a dedicated hardware device designed to securely manage digital keys and perform cryptographic operations like encryption, decryption, and digital signing.
HSMs protect sensitive data and cryptographic keys from being exposed to unauthorized access or tampering.
HSMs are widely used in industries requiring strong data protection, such as banking, healthcare, and government sectors.
It is a root of trust that protects services we use every day like banking and websites. Cryptocurrency, medical device national identity cards, mobile payments, and any more
Integration benefits
Integrating Data power with HSM brings several benefits as follows.
Enhanced security
HSMs provide a secure environment for key management, ensuring the confidence and integrality of cryptographic operations.
Improved performance
Offloading cryptographic operations to HSMs can significantly enhance the performance of data power by leveraging dedicated hardware acceleration
Compliance adherence
HSMs help meet security and compliance requirements, such as PCI-DSS, HIPAA, and GDPR, by providing a trusted platform for key management and cryptographic operations.
Secure key management
They provide a tamper-resistance environment for key protection ensuring that cryptographic keys are securely stored and accessed only by authorization process.
Secure Authentication
HSMs enable secure authentication by storing and managing digital certificates and credentials. This ensures the authenticity of users and devices in networked environments.
Digital signatures
HSMs are used for generating digital signatures, which verify the authenticity and integrity of electronic documents and transactions. This is crucial in applications like electronic contracts and secure email notification
Compliance and Regulatory Requirements
HSMs help organizations meet regulatory compliance requirements, such as those stipulated by PCI-DSS (Payment Card Industry Data Security Standard), HIPAA (Health Insurance Portability and Accountability Act), and GDPR (General Data Protection Regulation).
Cryptographic Operations
These devices accelerate cryptographic operations, enhancing the performance of security protocols and algorithms. This is essential for maintaining the efficiency of the secure communication system.
Secure Execution of code
Some HSMs support secure execution environments for cryptographic applications, ensuring that sensitive operations are performed in a protected and isolated environment.
Cryptographic Key Backup
HSMs often offer mechanisms for securely backing up and recovering cryptographic keys, reducing the risk of data loss due to hardware failures or other disasters.